Category: Computing
-

Computer Security: 20 years of securing controls (or trying to): mitigations
We’ve seen in the past two Bulletins that control system cybersecurity is the black sheep of IT, a hard-to-change tanker’s course. Still, with significant daily damage of 250 000 USD for ALMA, the costs of falling to a cyberattack can no longer be ignored
-

Computer Security: 20 years of securing controls (or trying to): black swans and convergence
While eagerly expected by experts, the first dominant incident on control systems reported by the media was the Stuxnet attack of 2010 against the Iranian nuclear programme allegedly conducted by some secret services
-

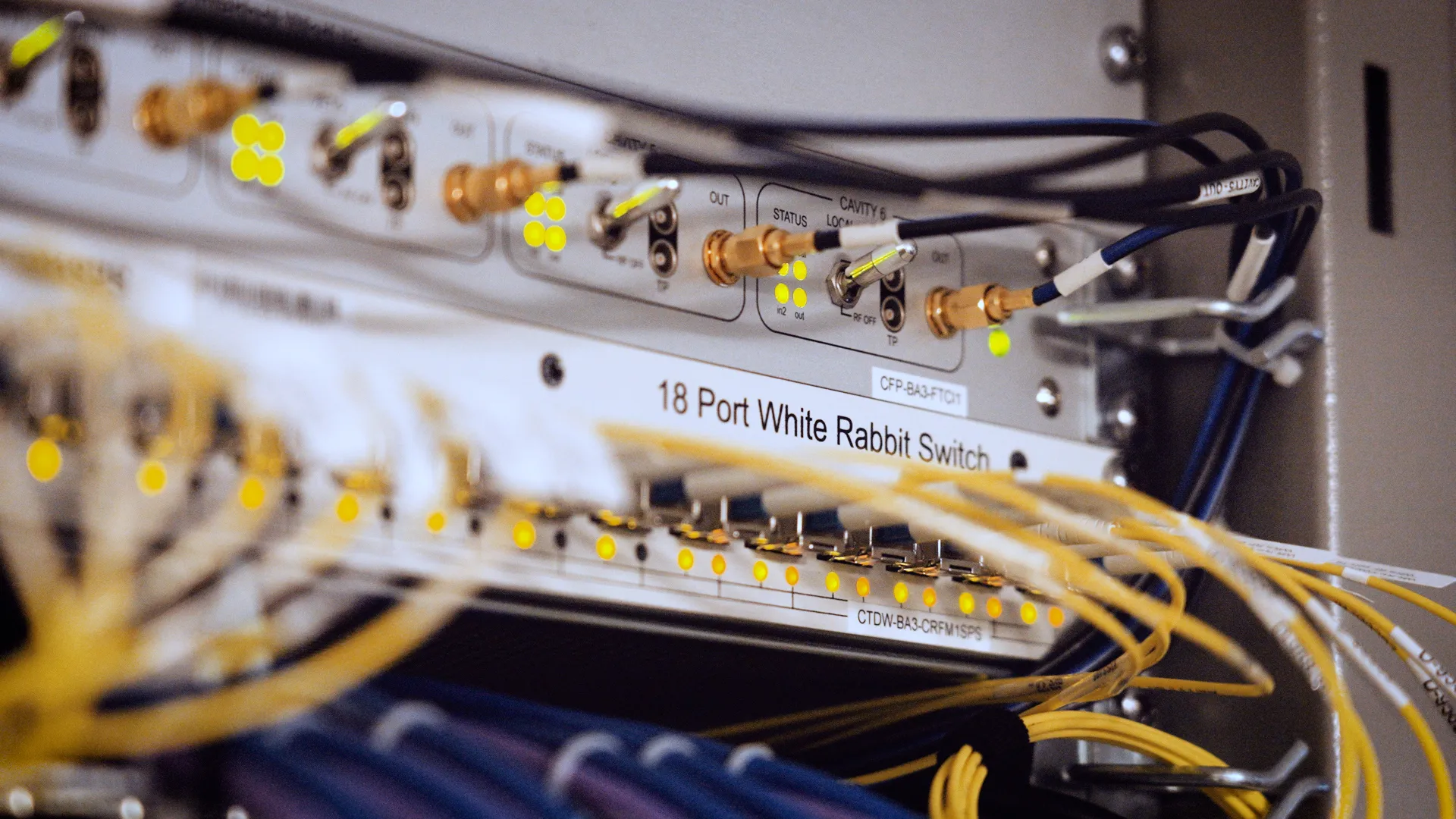
Computer Security: 20 years of securing controls (or trying to): nothing has changed?
20 years ago, control systems used to be stand-alone systems, usually decoupled from the larger enterprise networks, using their own network cabling infrastructures and programming languages dedicated to control systems. But no more…